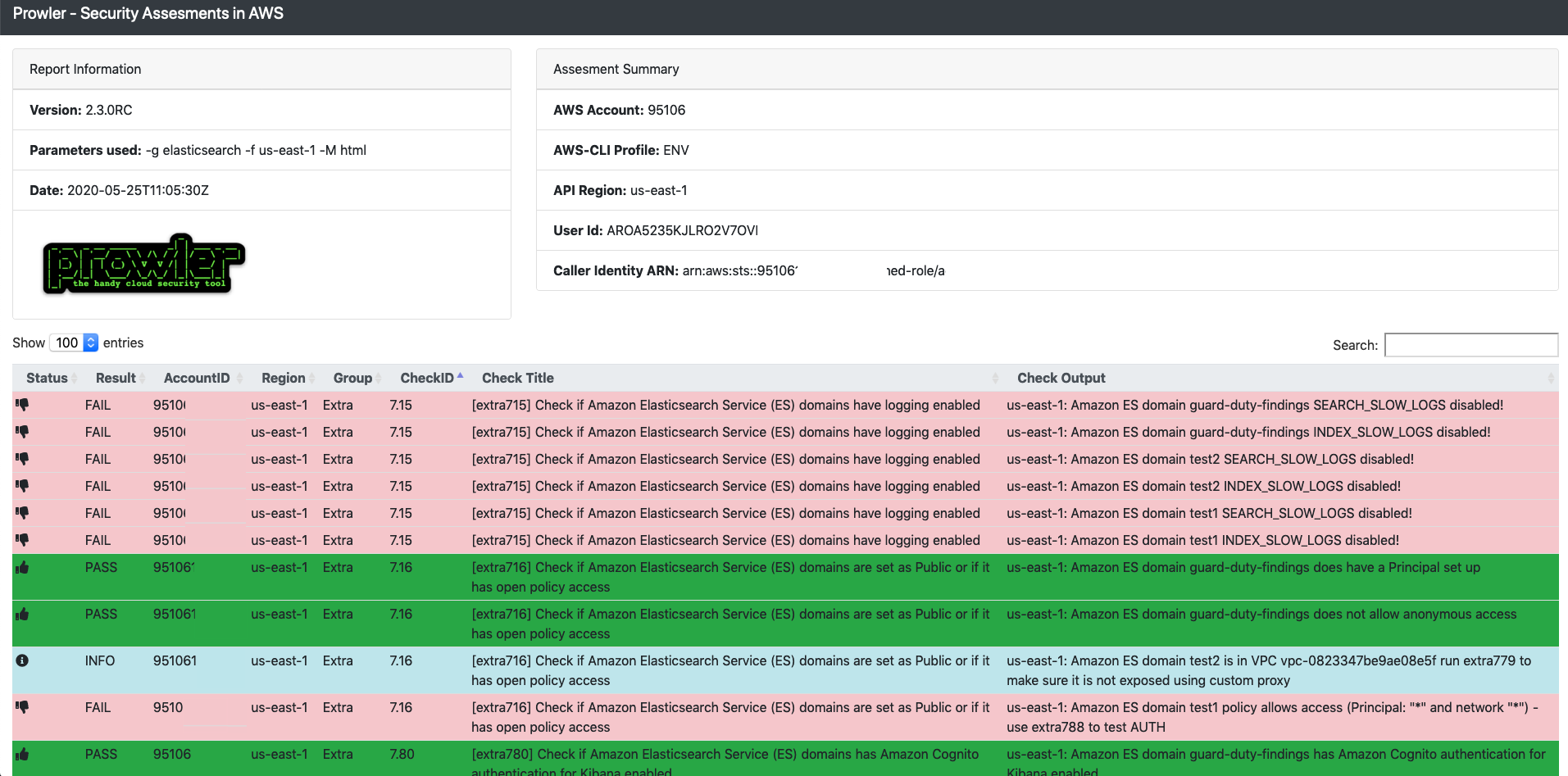
Top Security Scanning and Vulnerability Management Tools |AWS| | by Kubernetes Advocate | AVM Consulting Blog | Medium

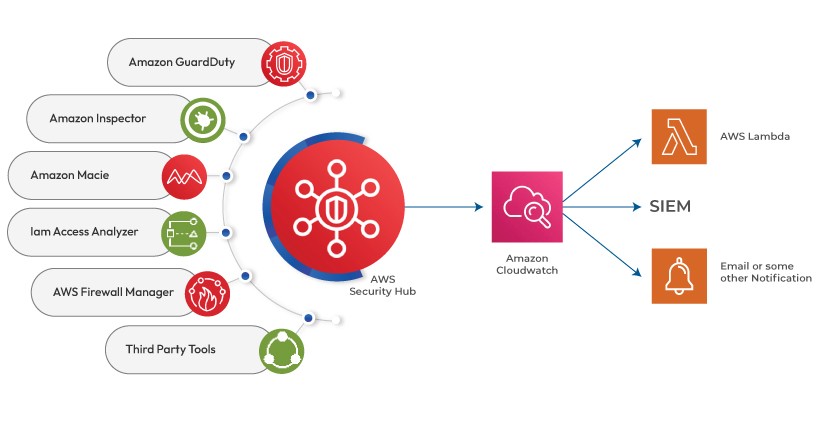
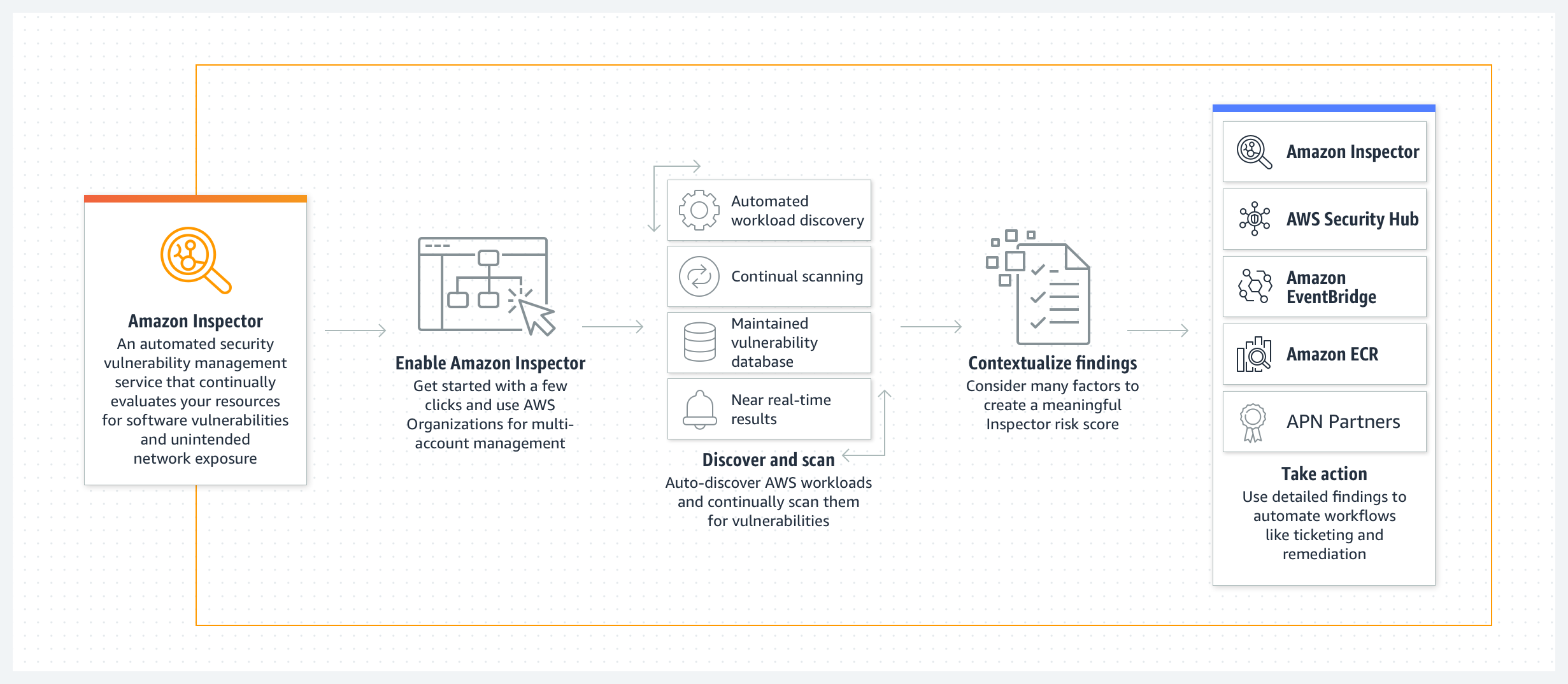
Automate security scans for cross-account workloads using Amazon Inspector and AWS Security Hub - AWS Prescriptive Guidance
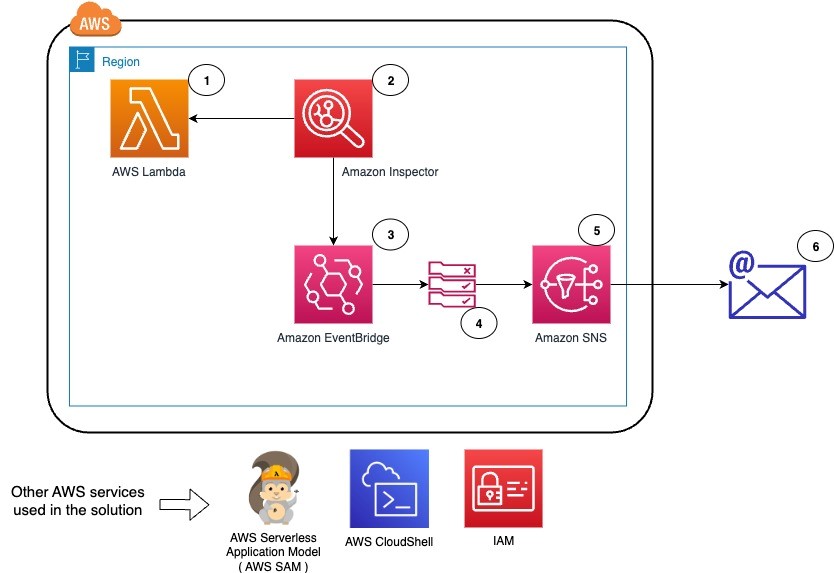
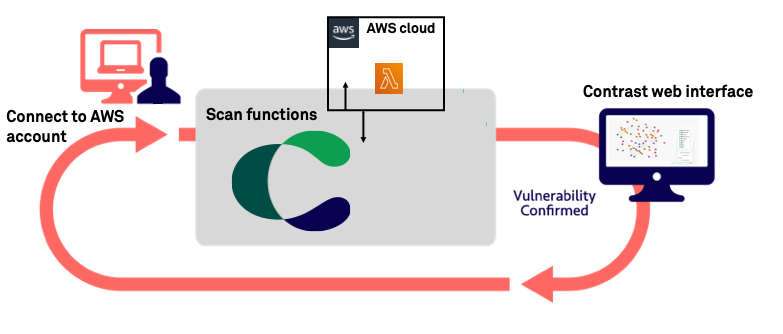
Perform continuous vulnerability scanning of AWS Lambda functions with Amazon Inspector | AWS Security Blog

Amazon S3 Malware Scanning Using Trend Micro Cloud One and AWS Security Hub | AWS Partner Network (APN) Blog
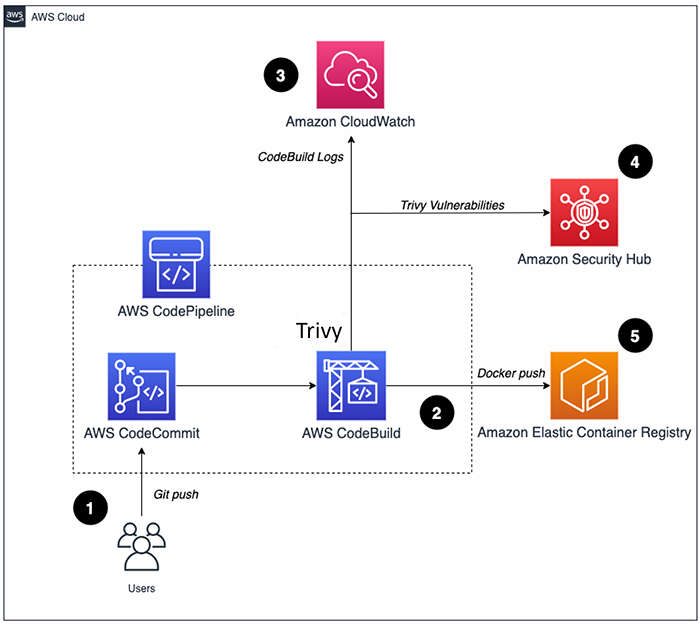
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog

Scanning Docker Images for Vulnerabilities using Clair, Amazon ECS, ECR, and AWS CodePipeline | AWS Compute Blog