
Angry IP Scanner | How Hacker's Scan a Network | Advance Scanning using Angry IP Scanner|| Angry IP - YouTube

Hacker Hand Using Abstract Padlock Fingerprint Scanning Interface On Blurry Background. Access And Hacking Concept. Multiexposure Stock Photo, Picture And Royalty Free Image. Image 127352647.

Premium Photo | Hacker cyber attack scanner digital business password cloud document online database technology in a hood on dark backgroundsecurity internet protection concept

Hack Like a Pro: Perl Scripting for the Aspiring Hacker, Part 2 (Building a Port Scanner) « Null Byte :: WonderHowTo









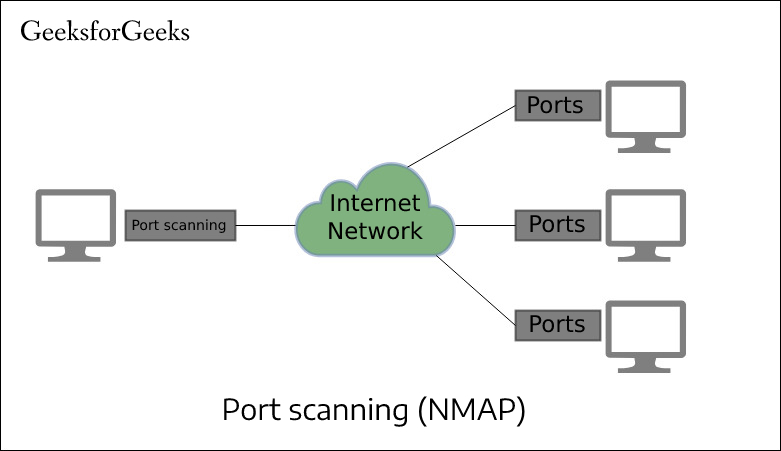




![Guida] Nmap: introduzione al tool usato dagli hacker per le analisi di rete Guida] Nmap: introduzione al tool usato dagli hacker per le analisi di rete](https://www.lffl.org/wp-content/uploads/2021/09/nmap.png)

